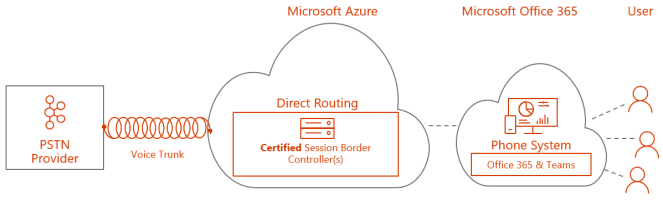
Today Microsoft Teams Direct Routing was announced as General Available. This is the means for you to bring your own SIP trunk to Microsoft Teams using only a standard SBC. Today AudioCodes and Ribbon are certified SBC’s for Direct Routing and more are in the works. There are three flavors to Direct Routing
Hosted in Azure!
Yes you read correct. AudioCodes has a certified SBC that now is supported in Azure, which means you can run your Direct Routing SBC in Azure as an appliance.
- AudioCodes Virtual Edition SBC is certified for Direct Routing
- Check out the AudioCodes whitepaper on how to install their SBC in Azure.
- As long as the SBC is certified and supported by the vendor to run in Azure, it is implied that Microsoft will support it as well, no official Microsoft link at the moment
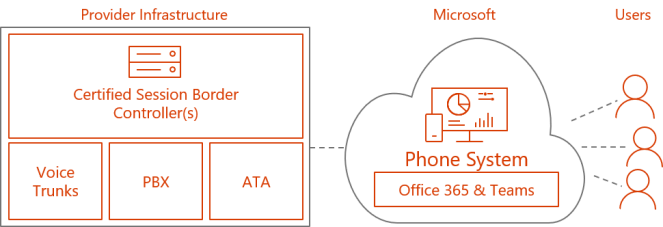
Installed in your datacenter connected to your PBX or SIP trunk
With Direct Routing you do not need any Skype for Business or Teams components installed in your datacenter to provide voice for your Teams users. All you need is a certified SBC, a public IP address and a public certificate to connect. Read my blogpost on infrastructure requirements for setting up Direct Routing in your datacenter

Hosted by a partner
One SBC can connect to multiple Office 365 tenants making this scenario scalable. This means you can consume native Microsoft Teams services from your own tenant and have a service provider host your voice connectivity.
Thoughts
I think Direct Routing will make Cloud Voice mainstream and it can be combined with Calling Plans where available, which means that you can freely choose how to consume voice. Being able to install the SBC in Azure means that anyone can now host and conenct their own sip trunk to Office 365. With the ability to either get this hosted or set up with next to no on-premises infrastructure you have a solution that can be consumed by most customer types from SMB to Enterprise.
References
- Read the official announcement at TechCommunity
- Check out my blog on infrastructure requirements explained for Direct Routing
- Plan Direct Routing
- Configure Direct Routing
- Migrating to Direct Routing
- User accounts in a hybrid environment with PSTN connectivity
- Configure a Session Border Controller for multiple tenants
- List of Session Border Controllers certified for Direct Routing

 Multi-Factor Authentication (MFA) in Office 365 is dependent on Modern Authentication which is oAuth 2.0 via ADAL that authenticates the user in Azure AD
Multi-Factor Authentication (MFA) in Office 365 is dependent on Modern Authentication which is oAuth 2.0 via ADAL that authenticates the user in Azure AD