Any Post starting with this disclaimer means that this post was not written by me however I liked it and added to my blog. I will also include the link to the original or similar post to provide credit to the original author
http://blogs.pointbridge.com/Blogs/schertz_jeff/Pages/Post.aspx?_ID=33#EntryTabs
Deploying an OCS 2007 R2 EDGE server can be confusing at times. I have been looking for the most cost effective way to deploy a consolidated EDGE server utilizing the least amount of NIC’s and public IP addresses. In the past when I have deployed EDGE server I have used separate NIC’s with publicly routable IP addresses to save myself some grief. I found Jeff’s blog very easy to understand and I am sharing an excerpt clarifying the different ways to deploy a consolidated EDGE server.
The documented, recommended, and unquestionably supported configuration is simply to deploy separate physical network interface cards which are connected to separate IP subnetworks. (This includes a single physical card with multiple ports; whatever physical configuration that allows you to plug two cables into the server and the host sees separate interfaces. Let’s not get silly here.) By definition this means that the internal and external subnetworks need to be uniquely different, which is typically found in a standard Perimeter Network located between separate firewalls.
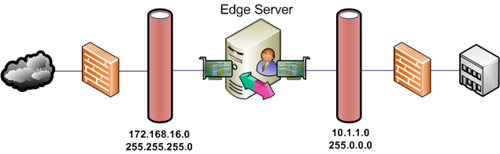
A simple Access Edge deployment utilizing NAT:
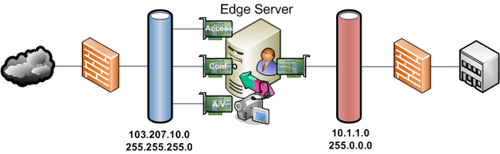
Or a consolidated Edge deployment with all three external roles assigned publicly routable IP addresses:

The above configuration only works for a consolidated Edge Server when all external IP addresses are on a public IP subnetwork, otherwise separate adapters connected to separate IP subnetworks would need to be used. The Access Edge and Web Conferencing roles can be co-located on the same same external interface using the same IP private subnetwork.
Here’s a consolidated Edge deployment using the least amount of public IP addresses:
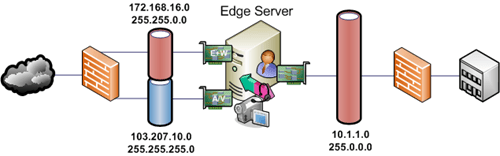
This can be expanded up to separate physical adapters for each external role in a consolidated Edge server, as shown repeatedly in the documentation, for enhanced performance and security. And if plenty of public IP addresses are available, then assigning each role a public address simplifies the configuration further: